The End of Safe Software? No, It's Not.
In the wake of Anthropic’s announcement of Mythos and Project Glasswing, and with the still-emerging blast radius of Aqua Security’s Trivy compromise, many security professionals are predicting the end of safe software.
We do not agree.
Instead, they simply highlight and reinforce:
- Security standards are rising, and proactivity breeds assurance
- Security basics are more important than ever
- Open source is resilient
The Attack Chains that Matter
What does this mythical LLM and an open source project’s compromise have to do with each other? The original vulnerable workflow in the Trivy project was identified by hackerbot-claw, an automated scanning tool run with the claude-opus-4-5 model. Those were simple GitHub actions vulnerabilities, though, not the headline vulnerabilities found by Mythos, right? Turns out that when researchers used prompts the right way, they were able to find the same vulnerabilities as Mythos with much smaller models.
The ongoing ramifications of Trivy, plus Project Glasswing, are reinforcing the urgency and importance for organizations to review and assess their security. Even for those who have applied patches to known vulnerabilities in the wake of Trivy, now with Mythos, the questions around vulnerabilities and responses need to be asked again:
- Do you know all the places where your dependencies and code are used?
- Can you triage, patch, and deploy fixes with confidence, all the way from development to production?
There Are Still Unknowns
Two months after Aqua Security disclosed that Trivy (an open source vulnerability scanning tool) was compromised, we still don’t know the full impact. What we do know is that a vulnerable GitHub Actions workflow leaked an access token, which was subsequently abused. This allowed the attackers to push code and overwrite 75 of 76 trivy-action GitHub tags. When users of Trivy’s GitHub action subsequently ran the action based on these compromised tags, their workflow’s secrets were exfiltrated.
So far, this has resulted in the compromise of additional open source projects, 350 GB of data stolen from the European Commission, and thousands of cloud environments trying to recover from compromise.
Anthropic almost opened Pandora’s Box with Claude Mythos, but instead rallied industry giants and foundations - including the Linux Foundation - to form Project Glasswing.
Mythos found 0-day vulnerabilities that have been hidden in plain sight for decades, one 27 years old in OpenBSD and one 16 years old in FFmpeg. There are thousands of additional critical and high vulnerabilities that are still working their way through responsible disclosure.
The aim of Project Glasswing is to mitigate the risks identified by Mythos and to secure the world’s most critical infrastructure.
Guaranteed Certainties
Tools such as Claude are here today, they’re being used widely, and will continue to become more powerful - for both users and attackers. Tools such as Trivy and other cybersecurity tools are obviously not going anywhere either. Here’s the thing, though: thousands more users of Trivy weren’t compromised because they were using read-only permissions for their scanning workflows. To avoid the FreeBSD NFS exploit found by Mythos, don’t use NFS if it isn’t needed.
Why are we pointing out permissions and NFS? Because, despite recent shocks and radical predictions, there is still strength in the basics of security, proactively layered for defence-in-depth.
And that brings us to our final point - open source is resilient, and there are strengths in open source that are often downplayed, if not overlooked.
The Resilience of Open Source
The original Trivy compromise had an exposure period of days, between March 19th and 22nd. When the attack spread to the LiteLLM Python package, the compromise was detected immediately by commercial tooling and was raised, communicated, and fixed by the community shortly after. The recent Axios NPM compromise was similarly detected and fixed in hours.
The speed of response and the number of resources available to assist in investigations and resolutions are features of open source software. The transparency of the software, its production processes, and maintenance increases trust. The open source community’s ability to respond, share expertise, and contribute to efforts is a valuable resource.
Each of these recently compromised projects is looking at, or has already introduced, ways to make trust verifiable. They are utilising techniques such as:
- GitHub’s immutable releases: locking down the release tags so they can’t be modified or reused
- SLSA build provenance: attesting to the origin of the software
- Trusted publishing: removing long-lived credentials and publishing from an auditable workflow with short-lived tokens all result in cryptographically verifiable trust.
Reality of Your Readiness
Even though many of these compromises have a short window of time to consume the malicious software, once it’s entered your organization, how do you trace its use? Can you respond to these kinds of events within hours, as the community does? Even if publicly compromised supply chains are quickly detected, organizations are still consuming other vulnerable software today.
For teams who are asking these questions, and who want to ensure they know where they stand, know where next they need to focus, ControlPlane’s Maturity Assessment provides an objective view of how your organization is truly performing across platforms, processes, security and governance. Click here to find out more, and to get in touch.
Related blogs
How LLMs Are Ending The Attacker-Defender Stalemate (And What to Do About It)
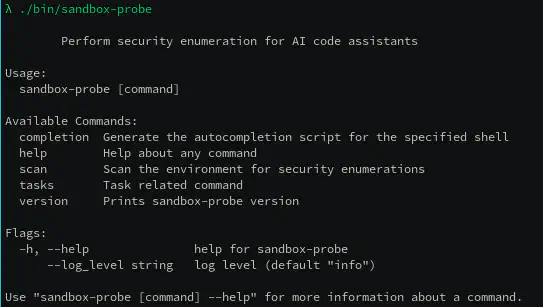
sandbox-probe: Putting AI sandboxing to the test

